Description of Active Actions in SM
As a result of executing a search query, active actions can be configured.
To view existing active actions in Smart Monitor, in the interface for creating and configuring a search job, select the Active Actions tab and click the Add button.
List of available Actions:
- Sending E-mail - Sends a message to the specified address. For more information, see here
- Creating an incident - Creating an incident in the
Incident Managermodule. For more information, see here - Event indexing - Writes the result of a query to the index. For more information, see here
- Recording in the DB - Writes query results to external databases
- Event logging - Writes the results of a search query to the
job_scheduler.logfile of theJob Schedulercomponent - MITRE ATT&CK® techniques - Tags events as triggers of techniques and subtechniques of the
MITRE ATT&CK®database and writes events to the index - MITRE ATT&CK® Risk Scoring Assignment - Fixes the risk score in the trigger
- Risk Score Assignment - Allows recording a risk score
- Script another search - Running a job from the
Job Schedule - Running the script - Run an existing script on the server
- Webhook - Creating an HTTP request to a remote server
Next, the existing active actions are reviewed, along with a description of the configurable settings.
Sending E-mail

Description:
- To - recipient's address
- Subject - email subject
- Sign - signature at the end of the email
- Body - message to be sent; it is possible to switch to HTML markup
- Trigger "Run Once" - runs the active action for all query results collectively; when this parameter is disabled, the active action will be applied to each individual query result
- Enable time - adds the server time at the moment of sending
- Enable table - adds a table with search results to the message body
- Send file - a CSV file with the search query results will be attached to the email
- Merge - merges the search query execution results into a single message
- Header Setup - configuration of service headers that will be sent in each email
- Headers - service header
- Values - one or more data written to the header
Using certain headers in settings is prohibited as they are reserved by the system. Such reserved headers include:
- Return-Path
- Received
- Resent-Date
- Resent-From
- Resent-Sender
- Resent-To
- Resent-Cc
- Resent-Bcc
- Resent-Message-Id
- Date
- From
- Sender
- Reply-To
- To
- Message-Id
- In-Reply-T
- References
- Subject
- Errors-To
- MIME-Version
- Content-Type
- Content-Transfer-Encoding
- Content-MD5
- Content-Length
- Received-SPF
Creating an incident

Description:
- Incident title - a short title used to identify the incident in the general list
- Severity - the importance level of the incident
- Workflow - the associated workflow process
- Incident Description - a detailed explanation of the incident; the editor supports Github Flavored Markdown
- Drilldown Type - the format of additional information:
- Search – a search query containing either an event or additional incident-related information. For this type of detailed view, you can configure time boundaries to specify the period for which details should be displayed -Link - a URL to external information such as documentation
- Drilldown Text - search queries or URLs providing supplemental data. Allow time boundary configuration for search-type drill-downs. Unspecified boundaries default to the incident's original search job timeframe
- Index Suffix - allows storing incidents in a specific index. See index suffixes
- Trigger – configuration for when and how the active action is triggered
- Run Once – creates a single incident even if the search returns multiple results
- Incident Fields – configurable fields defined in the module settings
- Additional Fields – key-value pairs extracted from the search job results
- Inventory Linking – configuration for linking the incident to an Inventory object and selecting the relevant fields
- Local parameters – key-value pairs of local and global tokens used for dynamic data substitution
For the Severity field and all fields in the Additional Fields section, you can use tokens from the search job. See Using Tokens.
In the Fields from Search Results section, you must specify the fields returned by the search query and set their value to none. This will preserve the field names from the key input when viewing the incident.

Event indexing
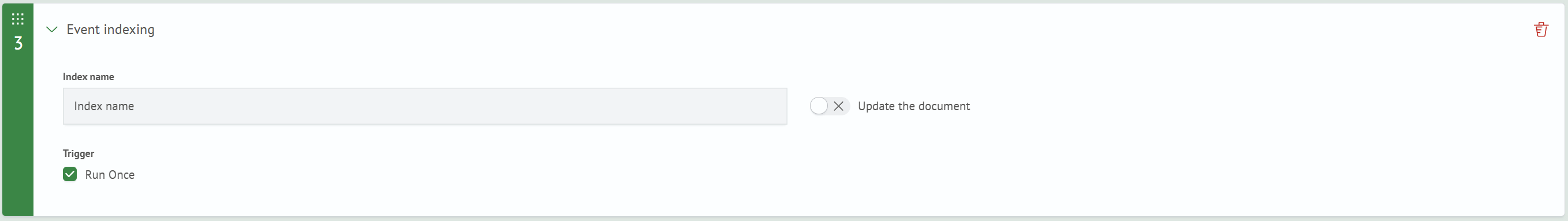
Description:
- Index name - index name
- Update the document - if the parameter is enabled, the document is updated every time a request is executed, otherwise a new one is created
- Trigger "Run Once" - if enabled, this Action will be performed only for the first search result, otherwise - for each query result
Recording in the DB

Description:
- User - identifier of the JDBC user for database authentication
- Connection - identifier of the JDBC connection to the database
- Table name - a database table to record the results of a search query
- Trigger "Run Once" - if enabled, this Action will be performed only for the first search result, otherwise - for each query result
Information about creating and managing JDBC connections and JDBC users is available in the Job Scheduler API article.
Event logging
No customization options.
MITRE ATT&CK® techniques
The result of the Action is written to the .smos_mitre-* index. The data in the index can be used to create incidents.

Description:
- Name - action name
- Rule - name of the correlation rule for which this Action is configured
- Layer - selecting the created layer in MITRE ATT&CK®
- Technique - list of MITRE ATT&CK® techniques that are categorized for this incident
- Severity - severity events (low, medium, high)
- Trigger "Run Once" - if enabled, this Action will be performed only for the first search result, otherwise - for each query result
- Additional Fields - creating additional key-value fields in the incident card
If you use the MITRE ATTACK Technique Recording action after the Create Incident action, the incident_id field containing the identifier of the incident created by the same trigger event will be automatically added to the record document.
Risk Score Assignment
Allows assigning a risk score to an object or event.

Parameter descriptions:
- Score - The number of risk points
- Index - The index where risk score assignment events will be stored
- Result Fields - Key-value fields for using parameters from the query
- Scoring Type - The scoring type to which the assigned risk score will belong
MITRE ATT&CK® Risk Scoring Assignment
The result of the Action is written to the .smos_risk-* index. Allows you to assign a risk score, for example, to a category of users or hosts for performing controlled actions. The data in the index can be used to create incidents.

Description:
- Name - action name
- Risk category - by what entity the calculation is made (system and/or user)
- Risk score - number of risk score per operation
- Fidelity - weight of the risk score. Accepts a value from 0 to 1
- Trigger "Run Once" - if enabled, this Action will be performed only for the first search result, otherwise - for each query result
- Additional fields - creating additional key-value fields in the incident card
Script another search

Description:
- Select Action - selecting the name of an existing job in
Job Scheduler - Trigger "Run Once" - if enabled, this Action will be performed only for the first search result, otherwise - for each query result
Running the script
The Script Execution active action is used to automatically execute shell and Python scripts on a remote server when rules are triggered.
The script must be located on a server with running Smart Monitor Remote Execution, which is specified in the Job Scheduler component settings.
Information about SME-RE setup is available in a separate section of the documentation.
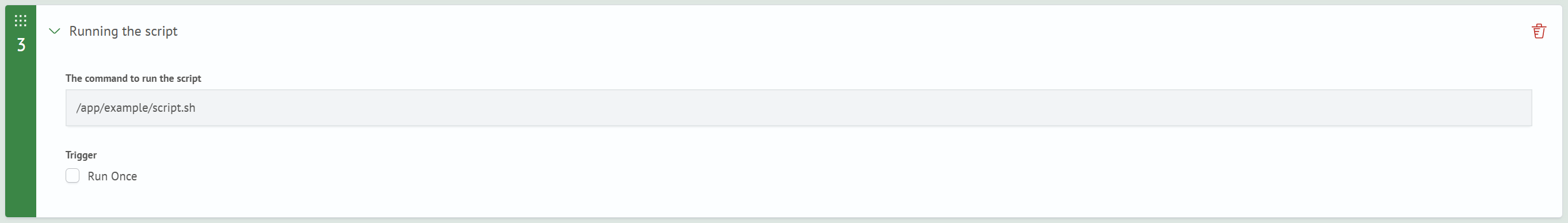
Parameter description:
- The command to ru the script - the command that will be executed on the remote server. It can contain an absolute path to the executable file or an arbitrary shell command
To execute Python scripts, you must explicitly specify the Python interpreter being used, for example:
python3 /app/smart-monitor/utils/scripts/test.py
Additional parameters (command line arguments) can be passed after the script name, for example:
python3 /app/smart-monitor/utils/scripts/test.py --index logs-* --limit 100
- Parameter "Run Once" - when enabled, the active action is executed once for the entire query result. When disabled, the action will be applied separately to each query result
Webhook
Can be used to write search job results to an external system using HTTP requests.

Description:
- Protocol - selecting the http/https protocol
- Host - address of the server getting requests
- Port - port of the server getting requests
- Request Action - type of request to the server (GET, POST, PUT, DELETE)
- Request - the path to the resource from the address bar after the port. For example,
path/to/sourcein the string https://example.source:443/path/to/source -
- Trigger "Run Once" - if enabled, this Action will be performed only for the first search result, otherwise - for each query result
- Params - used to pass parameters in the address bar. Specified as a key-value pair. Example:
parameters
?param1=value1¶m2=value2in this string:https://example.source:443/path/to/source?param1=value1¶m2=value2 - Authorization - parameters for authorization on the server getting the request
- Headers - can pass the headers to the receiving server as a key-value pair. For example, you can pass headers: User-Agent, Cookie, Authorization
- Body - body of the request
- SSL/TLS - enables the use of connection encryption protocols