Installing OpenSearch and Smart Monitor
General information
The OpenSearch installer must be run as the root user, specifying the path to it:
$ /opt/smart-monitor-installer/opensearch/install.sh
Together with OpenSearch, Smart Monitor Engine and its component Smart Monitor Engine Remote Execution (SME-RE) are installed. SME-RE is used for remote execution of Python scripts, in some cases a storage for intermediate script data may be required, in such cases the memcached package installation may be needed. For OpenSearch and SME-RE, the default owner is opensearch and the group is opensearch.
When deploying a cluster, you should consider the number of nodes with the master role, it must be odd to avoid voting problems (split brain issue).
Initial role setup
When creating a cluster with SSL, the Security plugin initialization in OpenSearch creates system indexes. The first cluster node must have master and data roles to ensure this initialization.
If initially it was planned to use only the data role without master, you should perform the following steps:
- Install the first cluster node with
masteranddataroles - Install the next cluster node with
masterordatarole - Use the
elasticsearch-node repurposeutility to change the roles of the first cluster node
You can read more about the elasticsearch-node repurpose utility in this article.
Installing main directories
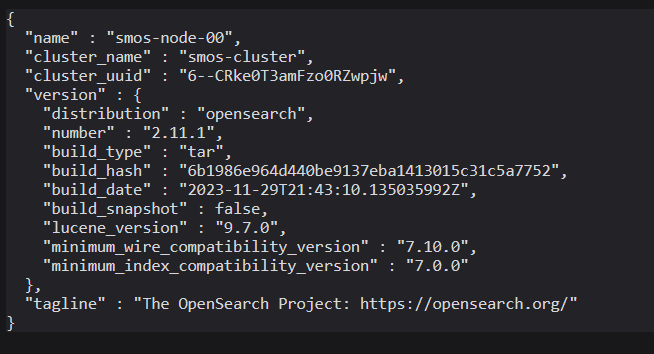
At the first step, system analysis is performed and if there is already an installed and running instance of OpenSearch or ElasticSearch, it may issue a warning:

In the image above, the found installation archive and OpenSearch version to be installed are also visible. The default action is to cancel the installation, to continue the installation you need to enter y. After this, running instances will be stopped.
At the first step, the main installation directories are set, the Smart Monitor license is specified and whether memcached should be used. We recommend storing all files related to Smart Monitor in one directory /app/, this will simplify further maintenance.
If you are performing a test installation and plan to install all Smart Monitor components on one server, then you must specify separate directories for each component.
The following set of parameters is requested at this step.
| Parameter | Description | Default value |
|---|---|---|
home directory | OpenSearch installation directory | /app/opensearch |
conf directory | Configuration files directory | /app/opensearch/config |
data directory | Directory for storing indexed data | /app/data |
logs directory | Logs storage directory | /app/logs |
Smart Monitor license path | Full path to Smart Monitor license file | |
Is memcached needed | If you plan to use memcached, you need to select y to enable and configure it, memcached must be installed before this moment |

After entering the data, the script will request confirmation of the correctness of the input, confirm by entering y and pressing the Enter key. The installer will analyze the existing directories and if they are not empty, it will issue a warning again:

If you continue, then all content of the specified directories will be deleted without possibility of recovery!
To continue the installation, you need to enter y again and press the Enter key.
Installing cluster and current node parameters
At this step, basic parameters for OpenSearch are entered.
| Parameter | Description |
|---|---|
Node name | Name of the current OpenSearch node |
Node roles list | List of roles of the current OpenSearch node, listed through comma with space, it is worth noting that in the cluster there must necessarily be master and data roles (or master, data_content and data_hot), i.e. if the cluster consists of one node, it must include these roles |
Node routing mode | If you plan to use multi-level data storage (hot-warm-cold), you can specify the required level for this node here |
Bind address— IP address of the interface on which OpenSearch will be attached, by default all available network interfaces are listened to (0.0.0.0), there is an opportunity to specify multiple IP addressesOpenSearch cluster name— cluster nameCluster discovery seed hosts— IP addresses of nodes with master role (if you plan to deploy a cluster of multiple nodes, this setting must be the same on all nodes and indicate external IP addresses), you can specify multiple IP addresses in quotes separated by commas, we recommend using odd number of nodes withmasterrole, otherwise there may be problems with voting within the clusterJVM heap size— amount of memory in GB allocated for OpenSearch JVM, this parameter should not exceed half of the free RAM on the server, the parameter sets-Xmsand-Xmxvalues for Java. Less than 4GB is not recommended to specify to maintain performance and speed of operation.

Cluster initialization
At this stage, the parameters for initial cluster initialization are set.
Is cluster initialized— whether the cluster is initialized (when deploying the first node, you need to answer no (n) to perform initialization, when deploying all subsequent nodes —y)Final initial master node list— names or IP addresses in quotes of nodes withmasterrole, listed separated by commas.
For increased reliability, you can specify the full list of nodes with master role, including those not yet deployed. For most cases, it is sufficient to specify the current node (default value).
Final initial master node list - this parameter is needed only for initial cluster initialization. All listed servers with master role must be identical to the node names in the cluster.
The image below shows the deployment of the first node.

Setting password for admin user
Next, you are offered to enter a password for the admin user in OpenSearch. You can specify a password hash (at the end of this step a question is asked whether the entered sequence is a hash), or enter another sequence.

By default, if nothing is entered, the hash corresponding to the default password will be set: P@ssWoRdElastic.
Installing certificate parameters
When creating private keys, the RSA cryptographic algorithm with a length of 2048 bits is used and the sha256 algorithm is used to create a digital fingerprint. A self-signed CA certificate according to our algorithm is created for 3650 days, and admin and current instance certificates for 1095 days.
At this step, a self-signed Certificate Authority (CA) certificate is initialized and the current node certificate is created. You can specify an existing CA certificate and private key.
Do you want to use existing CA certificate— do you want to use existing certificate and key files? You can specify your own files or use the built-in algorithm. If you use the built-in algorithm, answerno (n)only for the first installation. For subsequent nodes, you should use files from the current configuration directory (by default:/app/opensearch/config/ca-cert.pemfor certificate and/app/opensearch/config/ca-key.pemfor private key)Do you want to use an existing CA certificate and private key to generate certificates and keys for this node?— if you chooseno, then you will need to manually provide all necessary certificates for the node to work, otherwise, by choosingyes, the remaining certificates will be automatically generated based on the certification center certificate and keyPath to CA certificate— path to the root certificate (the certificate must be the same on all Smart Monitor components)Path to CA key— path to the private key (the key must be the same on all Smart Monitor components)CN for node certificate— common name for the current nodeCountry for node certificate— country nameState for node certificate— state nameLocality for node certificate— city nameOrganization for node certificate— organization nameExternal IP— external IP address of the current node, which will be used for interaction with other components
Below is an example with specified existing CA private key and certificate:

After entering the data, you need to confirm the correctness of their input.
Configuration formation
At this stage, no actions are required from the administrator. The stage is conditionally divided into two points:
- Preparing temporary directories, performing checks, preparing templates
- Forming configuration files from the specified parameters
Creating certificates
At this stage, no actions are required from the administrator, private keys and certificates are created from the specified parameters.
Unpacking the archive and changing configuration files
At this stage, no actions are required from the administrator, the OpenSearch archive is extracted, configuration files extracted from the archive are changed, preparatory processes before system changes.
All operations until this moment were performed strictly within the installer directory and do not affect the operating system, you can view the ready-to-install set of files in the staging directory.
For this, the administrator will be asked for permission to continue the installation:
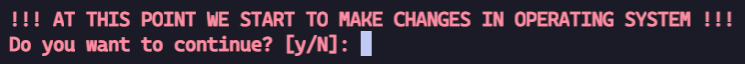
Confirm the changes to continue the installation by pressing the y key and then Enter.
Installation
At this stage, no actions are required from the administrator. Here several actions occur:
- Creating groups and users
- Creating directories
- Copying files and configurations
- Changing access rights to files and directories
- Applying SELinux security context
Launch and check
At this stage, no actions are required from the administrator and the following actions are performed:
- Starting
opensearchandsme-reservices - Checking service operability
- Applying security index
Configuring Job Scheduler
At this stage, no actions are required from the administrator and the configuration in the Job Scheduler module is configured.
Completing installation
At the end of installation, a firewall configuration message should appear as an example with firewalld, as well as a message about successful installation as in the image below. With any other form of installation completion, an error occurred and additional corrective actions are required.
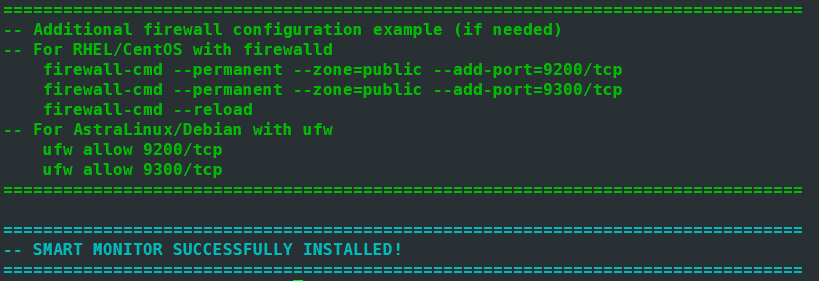
When the installer completes successfully, the node is deployed and ready for use. The opensearch and sme-re services should be running on it.
Services will be automatically started after rebooting the operating system.
Note that you need to configure the firewall for ports:
9200/tcp– port for accessing OpenSearch REST API9300/tcp– port for cluster node interaction
To check operability, open the page https://<your-server-ip-address>:9200 in your browser and use the default account: